Sales: +91 96000 06934
- Support
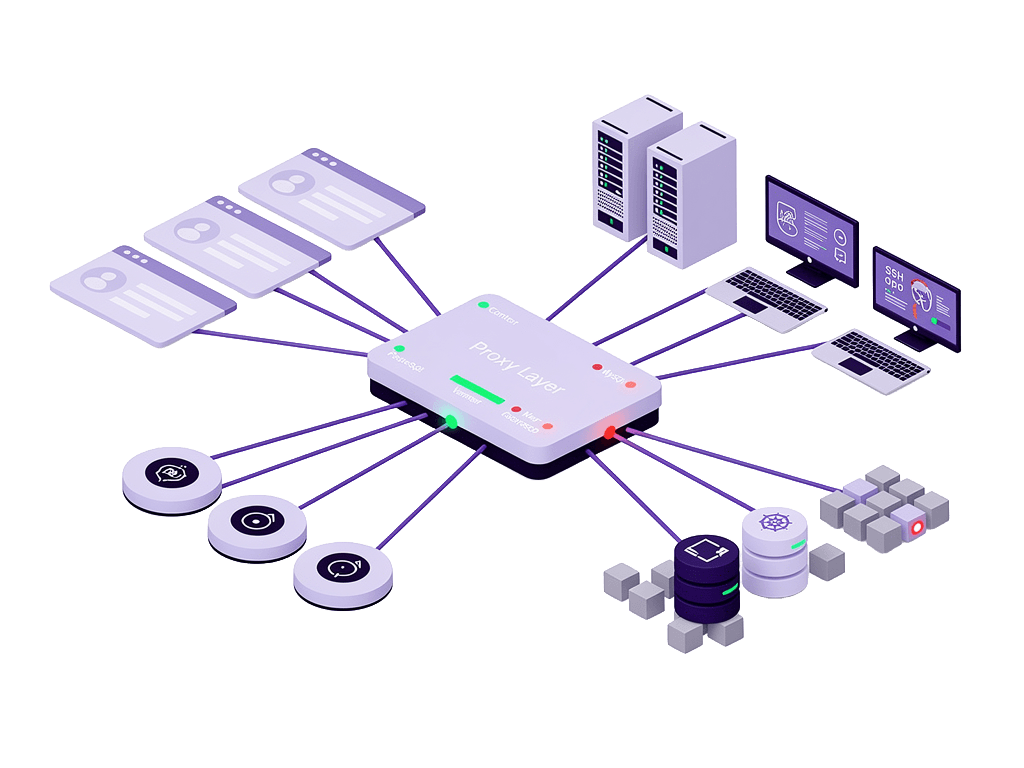
Every privileged session your team opens; to a server, a database, a Kubernetes cluster, or an RDP desktop; passes through AkkuReka first. Nothing reaches your infrastructure unseen.
Named for the line that cannot be crossed, AkkuReka enforces zero-trust verification at the point of every access request, proxies the session end to end, injects credentials silently from AkkuArka, and records everything; every command, every keystroke, every query, from the moment the session opens to the moment it closes.
A VPN gets your administrator to the network. It does not control what they do once they are there. It does not record their session, verify their device posture or location, inject credentials, or rotate them when the session ends. It leaves no forensic evidence of what happened.
Most organisations rely on VPNs, jump servers, or direct SSH access for privileged sessions, and these are approaches that were never designed for governance, compliance, or zero-trust enforcement. They provide connectivity and nothing else.
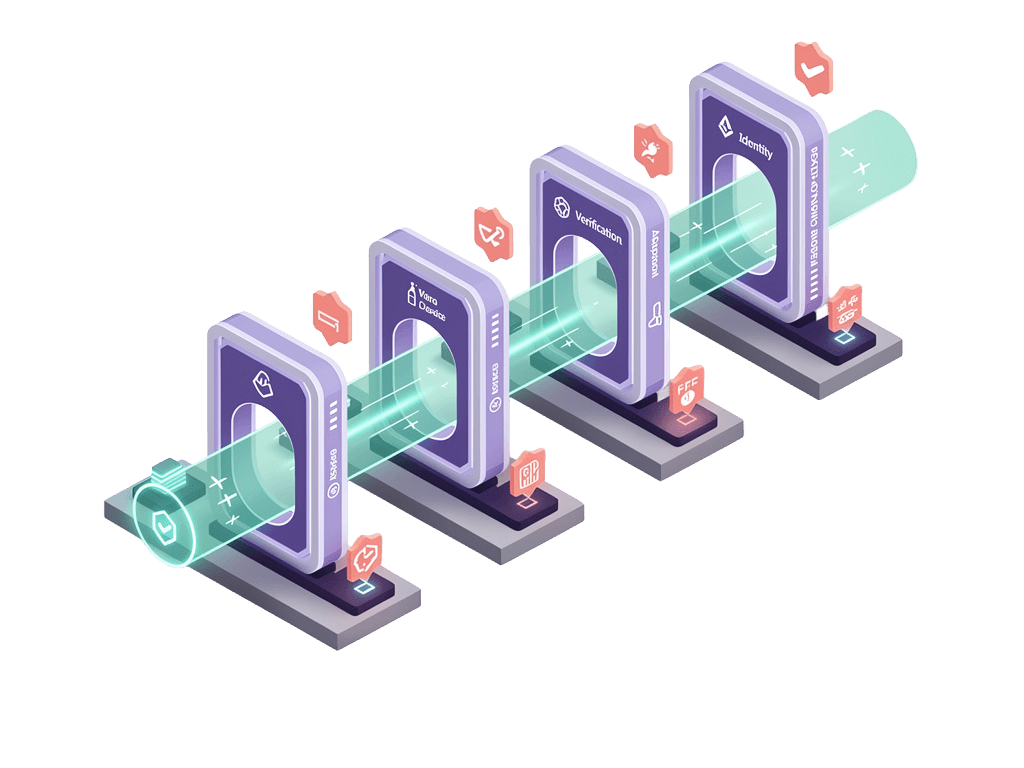
Seven control layers that govern every privileged session from request to closure.
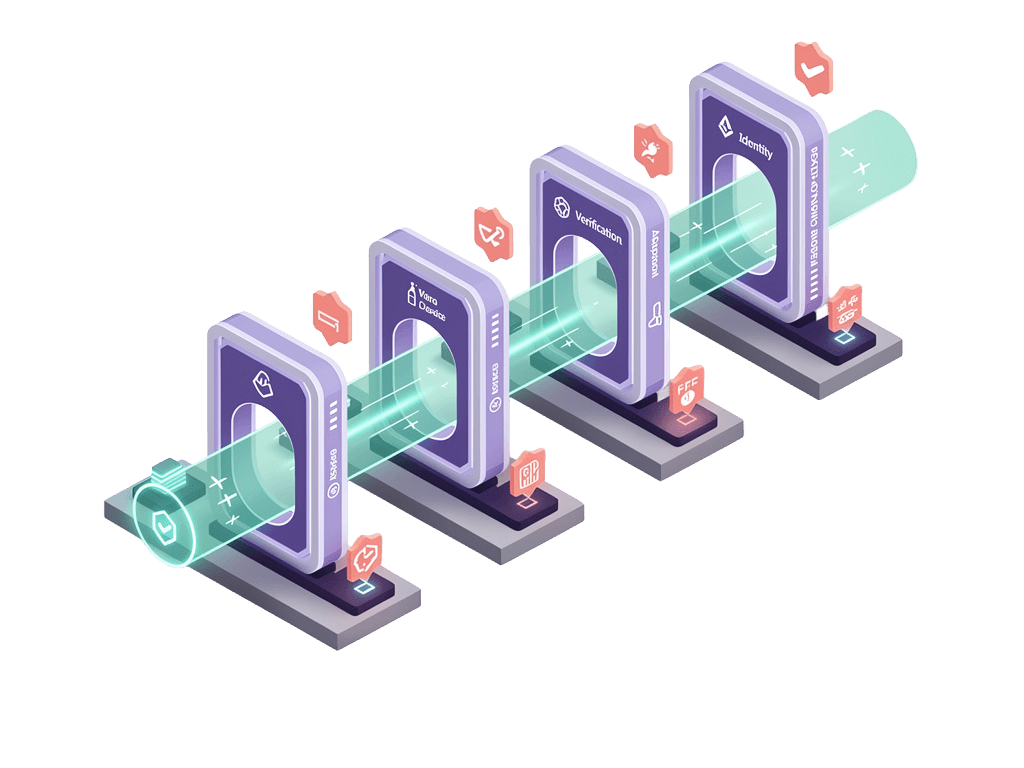
Before any privileged session opens, AkkuReka validates the request against your full access policy:
Every condition must be satisfied. If any check fails, the session is denied; before a single packet reaches the target system.
The governance gaps VPNs and jump servers leave wide open, closed by design.
Uncontrolled server access
VPNs and jump servers provide connectivity without governance. AkkuReka replaces uncontrolled access with a fully governed session proxy; every session verified, recorded, and auditable.
Credential exposure
Credentials are never transmitted to the user's device and never visible in any interface. AkkuReka's silent injection model eliminates this attack surface entirely.
Post-offboarding access
When a user is removed from Akku IAM, AkkuReka immediately denies all future session requests for that identity. The access path is closed the moment the identity is deprovisioned.
Compliance audit gaps
AkkuReka produces complete, tamper-proof evidence; session recordings, command logs, query logs, approval trails, and SMART Audit Trails; on demand.
Insider misuse and contractor overreach
Granular command control ensures users operate strictly within their authorised scope. Session recording ensures that anything outside that scope is captured.
All targets accessed through the same browser-based interface with no agents on endpoints and no VPN clients.
SSH Servers
Linux-based servers, full terminal recording, SMART Audit Trails, Granular Access Control
Windows RDP
Full screen recording with browser-based video playback, no RDP client required on endpoint
PostgreSQL
Transparent session proxy with query logging, per-session throwaway users via AkkuArka
MySQL
Transparent session proxy with query logging, per-session throwaway users via AkkuArka
MongoDB
Transparent session proxy with query logging, per-session throwaway users via AkkuArka
Kubernetes
Direct cluster access with full command capture
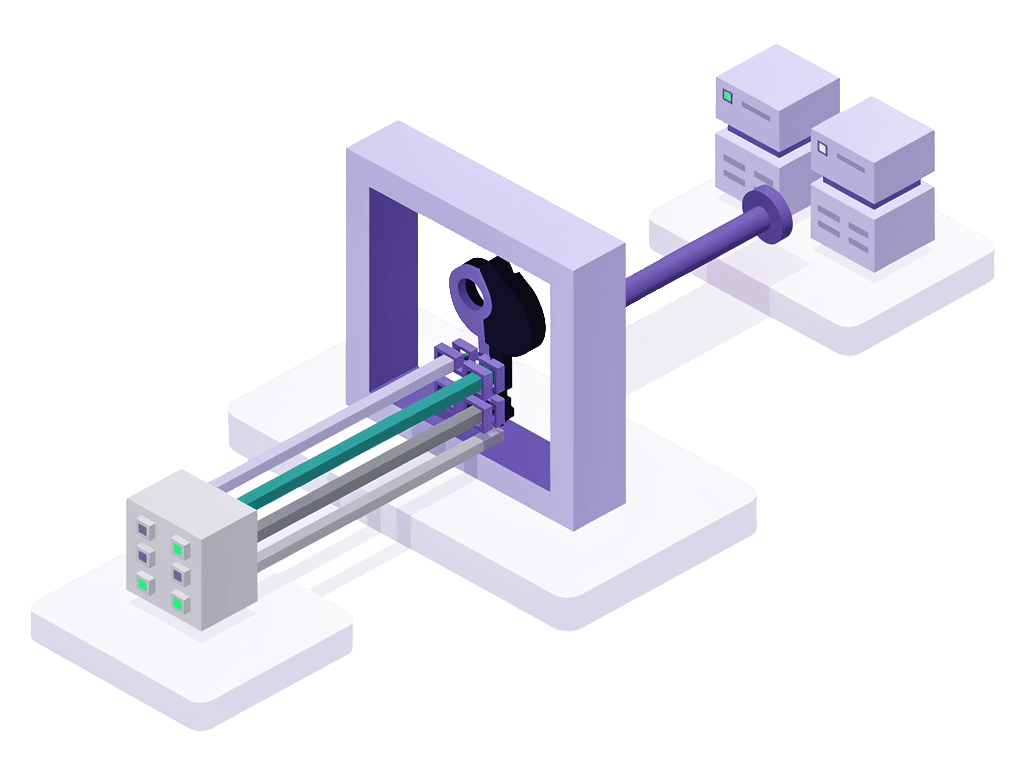
AkkuReka is the session layer. AkkuArka is the credential layer. Together they form the Akku PAM architecture: the line that cannot be crossed, and the source that never exposes itself.
AkkuArka holds every credential, rotates it, and supplies it only to AkkuReka. AkkuReka verifies every session, injects the credential silently, records everything, and signals AkkuArka to rotate when the session ends.
Neither component works effectively without the other. Together they ensure privileged access to your infrastructure is always governed, always recorded, and always credential-safe.
Learn how AkkuArka works
AkkuReka directly satisfies privileged session management requirements across:
Akku PAM is built for IT and security teams who need clear answers about how privileged access works, what the product does, and what it means for your infrastructure and compliance posture.
If you have a question that isn't covered here, please and we will be happy to address your queries.