Sales: +91 96000 06934
- Support
Your administrators need access to servers, databases, and Kubernetes. Your auditors need proof of everything that happened. Your credentials need to stay out of everyone's hands.
Akku PAM delivers all three through a zero-trust architecture built around two purpose-built components: AkkuArka, which generates fresh credentials for every session so users never see them, and AkkuReka, the session proxy through which nothing reaches your infrastructure unseen. Your team can be live in days, not months.
Shared root passwords. SSH keys that never rotate. Contractors offboarded from HR but are still technically able to connect. Developers with full server access when all they needed was to restart one service. No recording of sessions. No forensic trail. No way to prove, in a compliance audit or a post-breach investigation, exactly what happened.
This is the reality of managing infrastructure with a small IT team and no dedicated security headcount. The tooling to do it properly has historically been too expensive, too complex, or too slow to implement.
Akku PAM was built to close this gap for teams who need enterprise-grade privileged access control without a six-figure budget or a six-month implementation.
Most PAM solutions are password lockers. A credential sits in a vault. Your admin checks it out, uses it, checks it back in. The credential still exists. Someone still knows it. The risk doesn't disappear; it just gets slightly more organised.
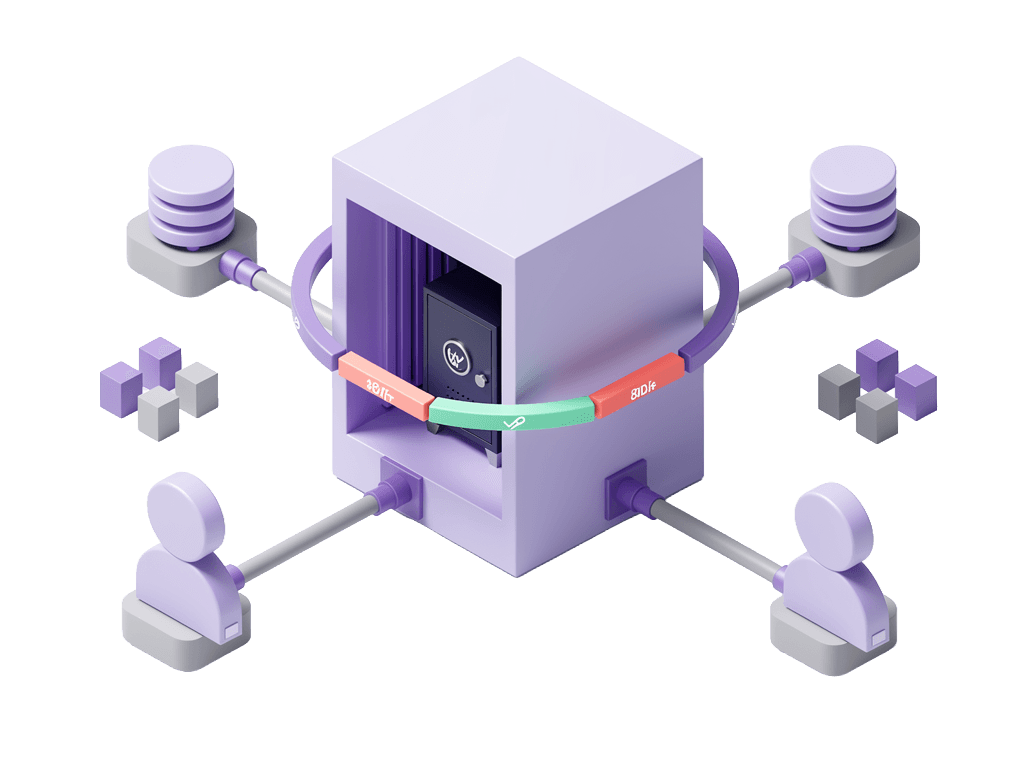
Akku PAM is built around a different model; two components that together ensure your credentials never leave the system, and every session is governed end-to-end.
AkkuArka is where every privileged credential originates. When a session is requested, AkkuArka generates a fresh credential for that session - a new password, a new user, or a new SSH key, depending on how the target system is configured. The credential is injected silently into the session by AkkuReka. No user ever sees it. No spreadsheet holds it. No team chat contains it. When the session ends, the credential ceases to exist. There is nothing to rotate, nothing to revoke, nothing left behind.
A unique throwaway user for each access request, with scoped permissions and automatic expiry. When the session ends, the user is dropped. The next request creates a new one. No shared database credentials. Ever.
AkkuReka is the session proxy through which every privileged access request must pass. Named for the line that cannot be crossed, AkkuReka enforces zero-trust verification at the point of every session:
Identity verification, device compliance, and contextual access policies are enforced by Akku IAM even before the request reaches AkkuReka. Only then does AkkuReka open the session; proxying the connection to the target system and silently injecting the AkkuArka credential. The user connects. The session is recorded in full. Every command is logged with an exact timestamp.
The target system never knows the real user's identity. The real user never knows the actual credentials.
Most PAM tools assume your databases and servers are reachable from the management network. In reality, many organisations have infrastructure that isn't, and shouldn't be.
Isolated networks; on-premise datacenters with strict firewalls, private cloud VPCs with no direct connection, air-gapped environments in regulated industries, are a common and deliberate security choice. They are also where most PAM tools break down, requiring either full product deployments inside every isolated zone or network rules that security teams will never approve.
Akku takes a different approach. AkkuArka and AkkuReka stay central, one vault, one proxy, one admin console, one audit log. A lightweight Akku agent is deployed inside each isolated network. The agent makes only outbound connections to the central system. No inbound firewall rules. No product stack inside the workload zone. No additional vault per environment.
The result: adding a new isolated environment takes minutes, not weeks. Your firewall stays exactly as it is.
How it works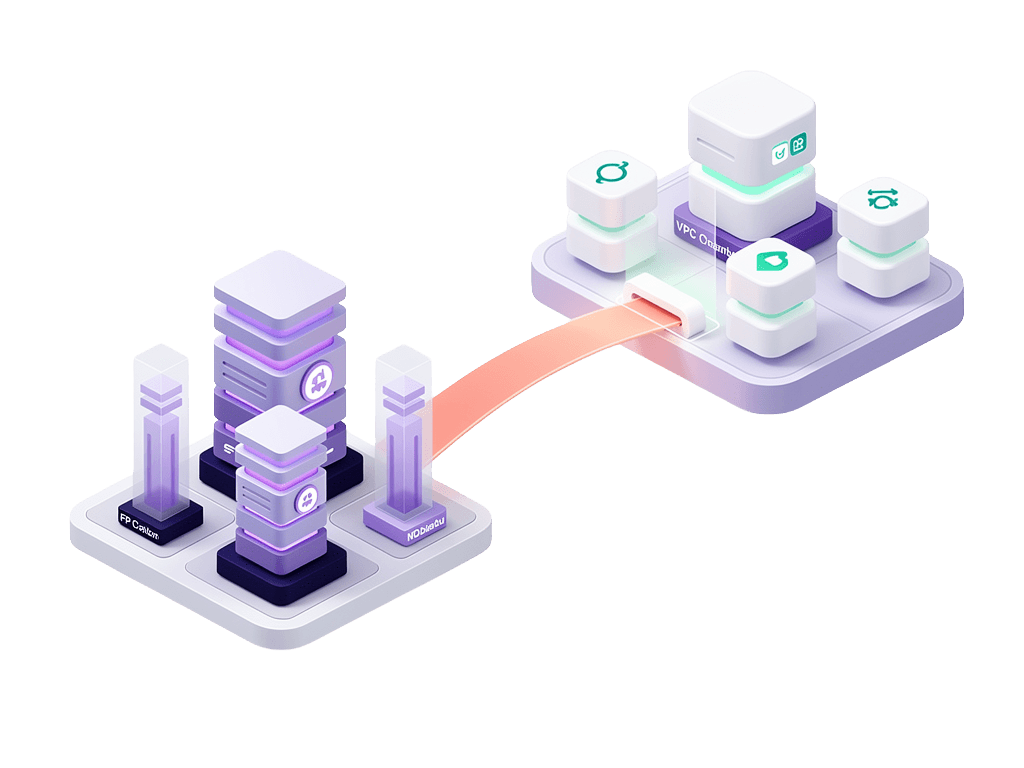
Every privileged credential is generated fresh at the point of request and expires when the session closes. Credentials are never given to users - AkkuReka injects them silently.
Learn More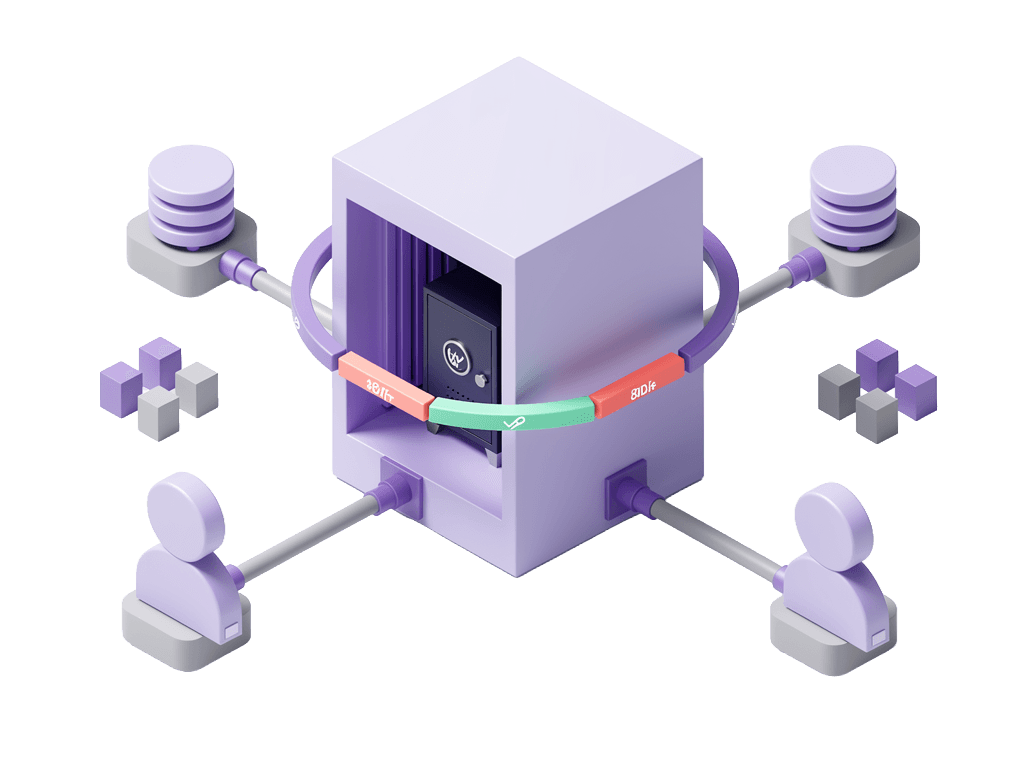
Access to SSH, RDP, PostgreSQL, MySQL, MongoDB, and Kubernetes using native clients — no VPN required, no credential exposure. Every session verified, proxied, recorded, and governed from a single point of control.
Learn More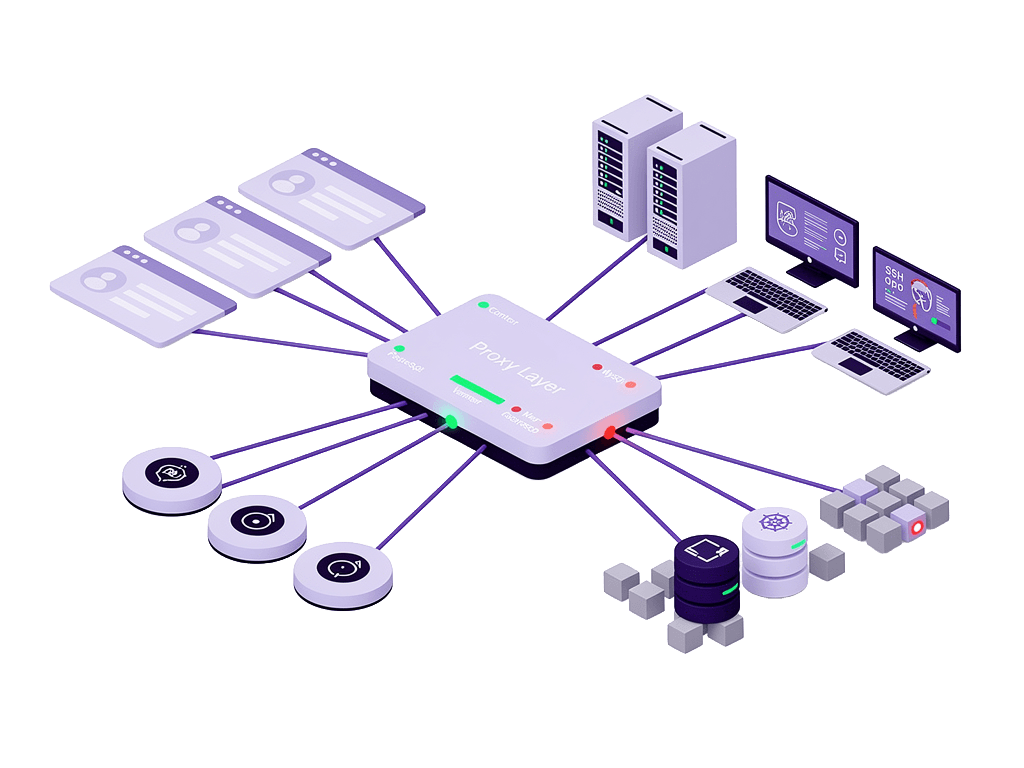
A lightweight outbound-only agent extends Akku PAM into isolated networks, private VPCs, and air-gapped environments, without inbound firewall rules, without a product stack in the workload zone, and without standing credentials inside the isolated network.
Learn More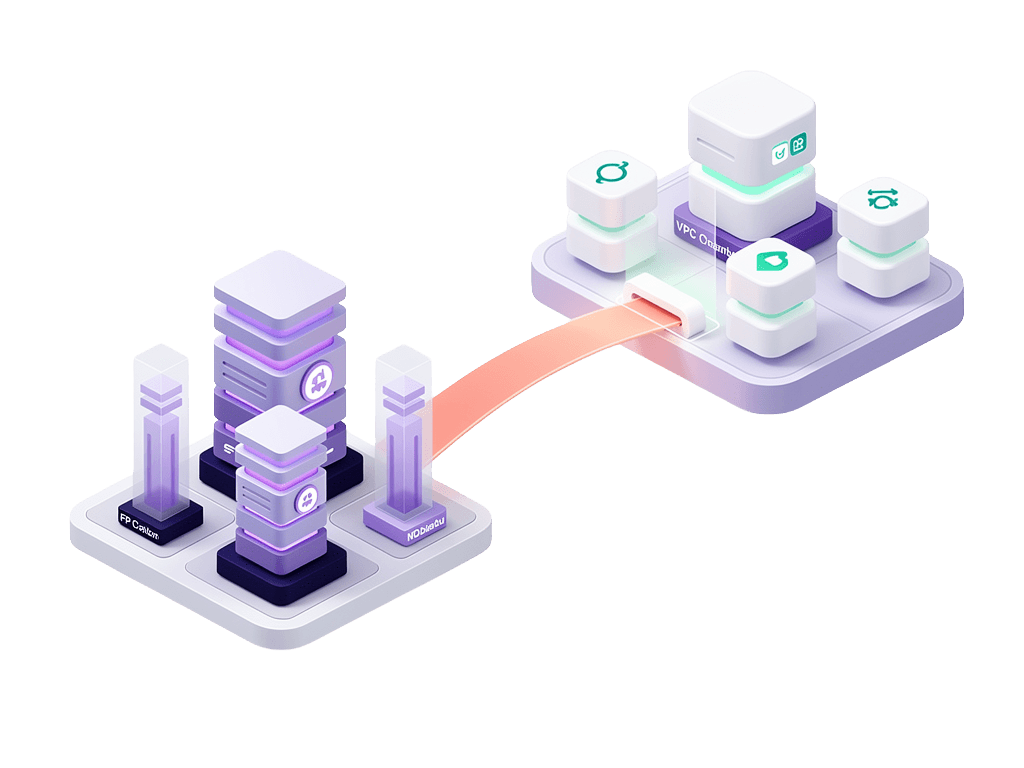
Every command executed in every SSH session captured with an exact timestamp; automatically, with no configuration required. Tamper-proof, centrally stored, searchable by user, command, server, or time window.
Learn More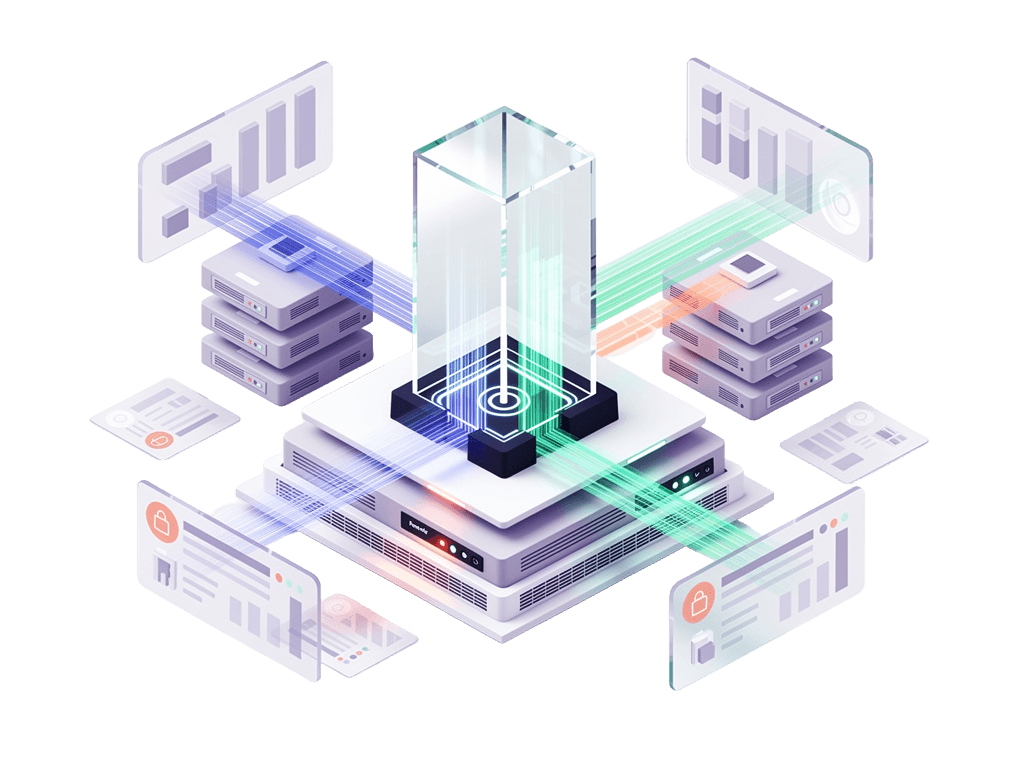
Define exactly which commands each user is permitted to run on each server. Commands not on the list are blocked at the point of execution; regardless of system privileges. Least-privilege enforcement at the command level.
Learn More
Enhanced access granted only when needed, only for the duration required. No standing privileges. Every access request routes through a configurable approval chain, with a full audit trail of who requested, who approved, and when.
Learn More
Adaptive MFA with behavioural anomaly detection. MDM device compliance enforcement. IP, geo-location, and time-of-day restrictions. The same IAM policy engine that governs your SaaS apps governs your servers.
Learn More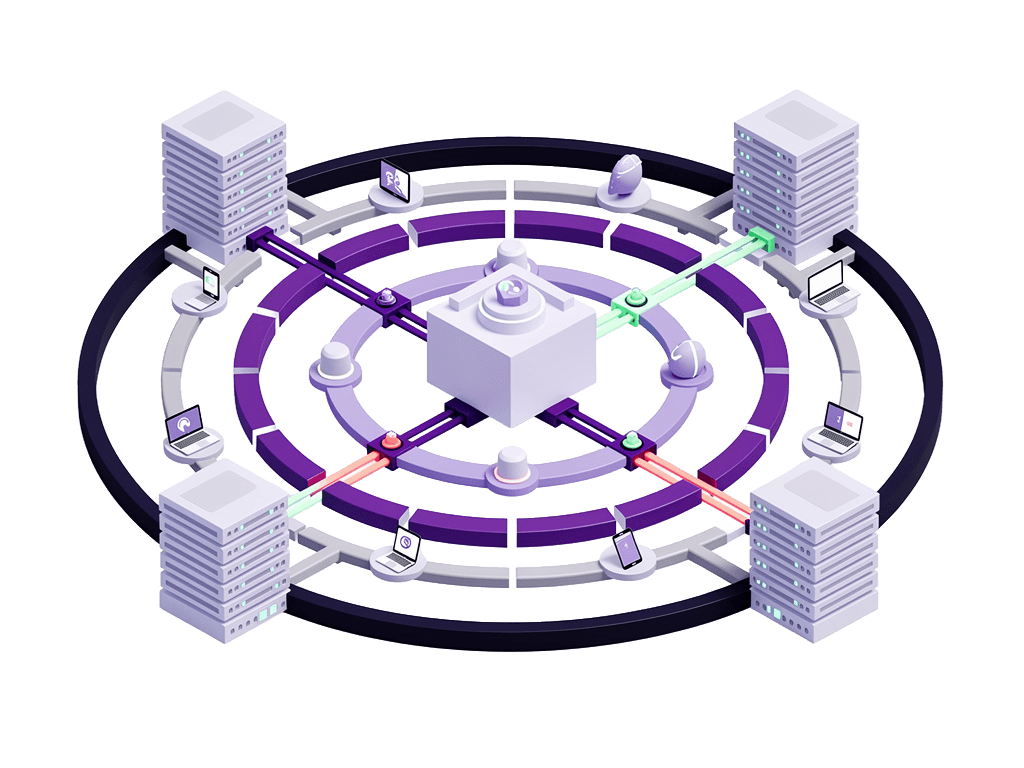
Assign privileged permissions by role, department, and attributes. Enforce Segregation of Duties. Detect and remediate SoD violations automatically. Permissions update instantly when roles change.
Learn More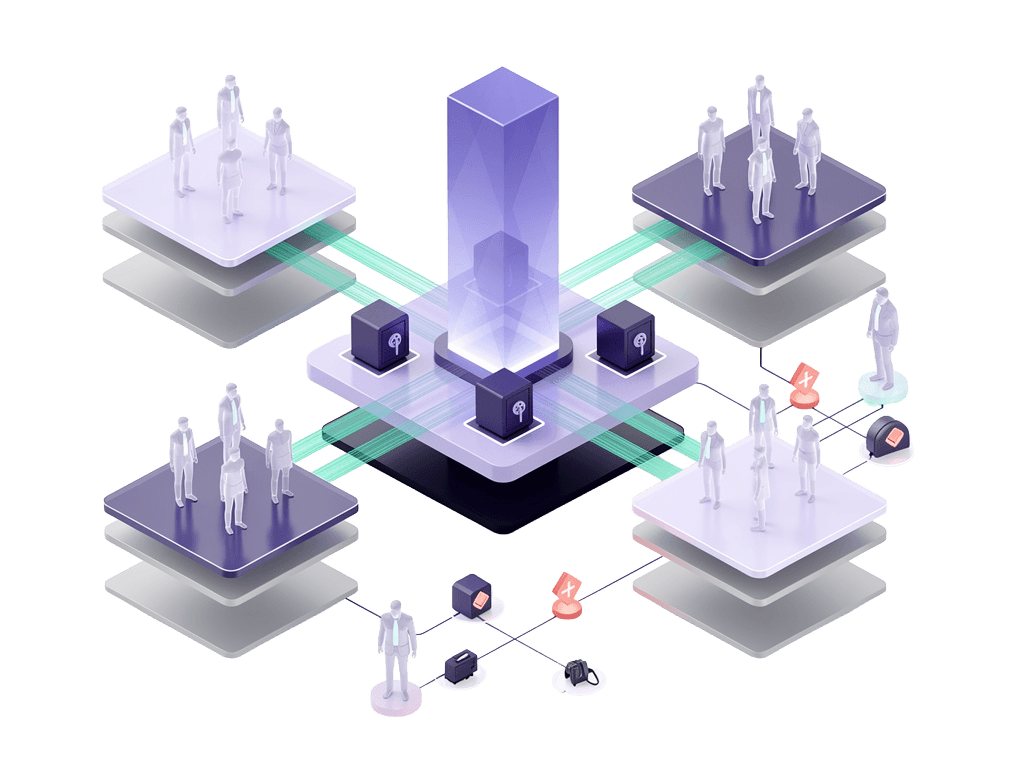
Most organisations end up managing identity in one system and privileged access in another. The integration between them needs to be built, maintained, and kept in sync. The gap between them is where offboarding failures happen.
Akku PAM is built on Akku IAM. They share one identity store, one policy engine, and one audit log.
Instant offboarding
Remove a user from Akku IAM and their privileged access is revoked at that moment. No separate PAM offboarding step. No gap window where an ex-employee retains server access because someone forgot to update a second system.
Unified contextual MFA
The adaptive MFA that governs your SaaS app access; device checks, IP restrictions, location policies, behavioural anomaly detection; applies identically to every privileged session opened through AkkuReka.
One audit log
Application access events and privileged server sessions appear in the same centralised log. One export covers your entire access history for compliance evidence.
One admin console
Manage identity, access policies, and privileged sessions from a single interface. No context switching between platforms.
Akku PAM is built to satisfy the privileged access requirements of every major compliance framework applicable to mid-market India:
When your auditor asks for evidence: session recordings, command logs, credential rotation records, access approval trails: Akku PAM produces it immediately. No manual evidence gathering. No scrambling. Export and done.
Akku PAM is built for IT and security teams who need clear answers about how privileged access works, what the product does, and what it means for your infrastructure and compliance posture.
If you have a question that isn't covered here, please and we will be happy to address your queries.